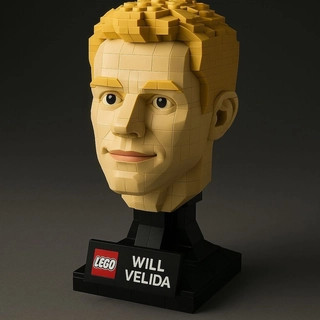
Will Velida articles - 145 total
Preventing Rogue AI Agents
Preventing OWASP ASI10 Rogue Agents in a .NET AI agent with behavioural constraints, kill switches, audit logging, immutable tools, and defence in depth.
Preventing Human-Agent Trust Exploitation in AI Agents
Preventing OWASP ASI09 Human-Agent Trust Exploitation in a .NET AI agent with medical disclaimers, tool-grounded responses, trust calibration, and confidence indicators.
Preventing Cascading Failures in AI Agents
Preventing OWASP ASI08 Cascading Failures in a .NET AI agent with resilience handlers, structured error responses, caching, and distributed tracing.
Preventing Insecure Inter-Agent Communication in AI Agents
Preventing OWASP ASI07 Insecure Inter-Agent Communication in a .NET AI agent with mutual authentication, signed messages, anti-replay, typed contracts, and protocol pinning.
Preventing Memory and Context Poisoning in AI Agents
Preventing OWASP ASI06 Memory and Context Poisoning in a .NET AI agent with session isolation, content validation, cache TTLs, and immutable configuration.
Preventing Unexpected Code Execution in AI Agents
Preventing OWASP ASI05 Unexpected Code Execution in a .NET AI agent with input validation, non-root containers, static tool registration, and runtime monitoring.
Preventing Agentic Supply Chain Vulnerabilities
Preventing OWASP ASI04 Agentic Supply Chain Vulnerabilities in a .NET AI agent with SBOMs, dependency pinning, kill switches, and zero-trust architecture.
Preventing Identity and Privilege Abuse in AI Agents
Preventing OWASP ASI03 Identity and Privilege Abuse in a .NET AI agent with Entra Agent ID, RBAC, federated credentials, and per-action authorization.
Preventing Tool Misuse in AI Agents
Implementing OWASP ASI02 mitigations against Tool Misuse and Exploitation in a .NET 10 AI agent built with the Microsoft Agent Framework.
Preventing Agent Goal Hijack in AI Agents
My side project (Biotrackr) now has an agent! It's essentially a chat agent that interacts with my...
Securing AI Agents: Implementing the OWASP Top 10 for Agentic Applications to my Health Data Agent
A practical walkthrough of the OWASP Agentic Top 10, implemented in a real .NET 10 AI agent built with the Microsoft Agent Framework.
Building a Health Data Chat Agent with Claude and the Microsoft Agent Framework
Using the Microsoft Agent Framework, we can build agents that interact with our data via chat...
How to Call Azure Services from an AI Agent Using Entra Agent ID and the .NET Azure SDK
Introduction: The Identity Problem with AI Agents AI agents are moving beyond simple...
Creating Entra Agent ID Blueprints and Identities with PowerShell and .NET
In Microsoft Entra Agent ID, we use agent identity blueprints to create agent identities and request...
Understanding Microsoft Entra Agent ID
As agents become more capable of making decisions, they require own identities to ensure proper...
How to Store Chat History Using External Storage in Microsoft Agent Framework
Chat history and memory allow agents to maintain context across conversations and remember user...
Using GitHub Models with the Microsoft Agent Framework
Almost a year ago, I wrote a blog post on how you could use GitHub Models with Semantic Kernel...
Exploring Azure SRE Agent Preview Service
I run various Container Apps as part of my personal health project. I want this project to be as low...
Building Remote MCP Servers with .NET and Azure Container Apps
A couple of months ago, I wrote a blog post on how you can create Model Context Protocol (MCP)...
How Tracing works in Azure AI Foundry Agents
Determining how Azure AI Foundry Agents makes decisions is important for troubleshooting and...
Building a Sports-Themed MCP Server Using .NET
I've lived in Melbourne for almost two years now, and throughout that time I've been trying to get my...
Using GitHub Models with Semantic Kernel
I'm making a conscious effort to deepen my knowledge on Semantic Kernel, and I just want an easy way...
Creating an AKS Automatic cluster with your OWN custom VNET in Bicep
In this article, I'm going to show you how to deploy an AKS Automatic Cluster within your own custom...
Creating an Azure Kubernetes Service lab environment with Bicep
In this article, I'm going to show you how to build an Azure Kubernetes Service lab environment with...
Custom Routing in Azure Virtual Networks
In order to control traffic flow within our Azure virtual networks, we can use custom routes, and...
Configuring Virtual Network Peering in Azure
In distributed Azure architectures, it's necessary to split up your virtual network infrastructure...
Understanding Private and Public DNS in Azure
To facilitate communication between resources in Azure deployed in virtual networks, we can use...
Configuring Public IP addresses in Azure
Azure Virtual Networks use private IP addresses which aren't routable on public networks. To enable...
Implementing a basic Azure Virtual Network with Bicep
Azure Virtual Networks (or VNETs) are the fundamental building block for private networks in Azure....
Using GitHub Environment Files for Actions Workflow Outputs
Sometime in the future, set-output commands in GitHub Actions will be depreciated! Here's how you can use Environment Files instead!