Articles by Tag #dataprotection
Browse our collection of articles on various topics related to IT technologies. Dive in and explore something new!
Cloud Security Protecting Your Data in the Digital Sky
In today’s digital era, cloud technology has revolutionized how businesses and individuals store,...
The Privacy Paradox
Every time you unlock your phone with your face, ask Alexa about the weather, or receive a...
How to Break Free from Restricted Mailbox Limitations
In today’s world, we are constantly connected to each other through various means of communication....
The Surveillance Crisis
When Match Group CEO Spencer Rascoff announced Tinder's newest feature in November 2025, the pitch...
The Impossible Promise
In December 2024, the European Data Protection Board gathered in Brussels to wrestle with a question...
Episode 3: Public RDS Detective — Finding Your Exposed Databases Before Attackers Do
Episode 3: Public RDS Detective — Finding Your Exposed Databases Before Attackers Do ...
Compliance in Financial Web Apps: How to Build Secure, Trustworthy, and Regulation-Ready Applications
“We had the perfect fintech app—until compliance brought everything to a halt.” That was the...
Oracle Autonomous Database: Backup Management, Event Notifications, and Data Guard Protection
Oracle Autonomous Database provides comprehensive data protection through automated backup...
The Invisible Tax: How Every AI Interaction Leaks Your Identity
TL;DR Every time you send a prompt to ChatGPT, Claude, Gemini, or any AI API, the provider...
Browser Fingerprinting: How Websites Track You Even With a VPN (And How to Stop It)
Most people think a VPN = privacy. Change your IP address, hide your location, and you’re safe…...
Why Hackers Want Your Personal Data (And How They Use It)
Photo Credit: Unsplash / FLY:D Keypoints Your personal data has real monetary value...
That €20,000 Cookie: A Guide to GDPR Compliance for Website Owners
It started with a cookie. Literally. A small tech startup in Berlin thought they had it all...
Stop Storing Plain Text Passwords! Use Bcrypt for Security
When building an application that requires user authentication, one of the worst mistakes you can...
Mastering Your Digital Privacy: A Comprehensive Guide to Online Protection
Mastering Your Digital Privacy: A Comprehensive Guide to Online Protection ...
How Small Businesses Can Implement Enterprise-Grade Security
In today’s digital-first world, data breaches and cyberattacks are no longer limited to large...
Your CMS Could Be Under Attack Right Now As I Write This — Here's How to Protect It
Picture waking up one day to discover your site — the cyber home you have spent months or years...
Cloud Security Challenges in 2025
Cloud adoption brings both opportunities and risks. Misconfigurations remain the leading cause of...
The Future of Cybersecurity Careers
Cybersecurity is one of the fastest-growing industries. AI and automation are reshaping job...
AI-Driven Cyber Attacks: The Next Evolution of Hacking
Artificial Intelligence is revolutionizing cybercrime. Hackers now use AI to automate phishing...
How Hackers Exploit IoT Devices
Billions of IoT devices expand the attack surface. Default passwords make them easy to...
The Rise of Deepfake Threats in Cybersecurity
Deepfake technology has become a cyber weapon. Attackers use fake videos to blackmail...
Privacy in Technology: Why It Matters More Than Ever
In today’s digital world, privacy is no longer optional , it is foundational. Every app we use,...
🔐 "My Password Wasn't Enough": Why You Need Multi-Factor Authentication Now More Than Ever
"But I had a strong password…" That was what my friend said, alarm in his tone, when he told me...
Zero Trust Security: Why It’s No Longer Optional
Traditional perimeter defenses are no longer effective. Zero Trust assumes no user or device is...
Quick Data Recovery using Snapshots - Amazon FSx for NetApp ONTAP
Let's look at what are Snapshots before we delve into the topic of data recovery. An ONTAP Snapshot...
Industry-Specific Data Security: Protecting Sensitive Data Before It’s Too Late
Why every business must tailor its security strategy to its industry Imagine this: A mid-sized...
Cybersecurity Essentials for the Modern Workplace
The modern workplace is more connected than ever—employees access data from anywhere, on any device....
Why You Need an SSL Certificate: Benefits, Security, and SEO
Why You Need an SSL Certificate: Benefits, Security, and SEO Most websites collect...
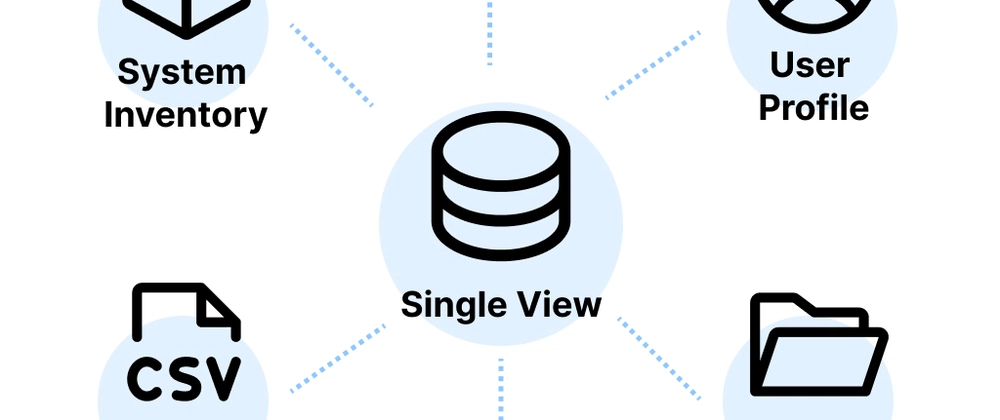
What Is a Single View?
According to Statista, 402.74 million terabytes of data are generated, imitated, and consumed daily....
Provide storage for a new company app
When building a new application in today’s cloud-driven world, storage is no longer just about saving...